How Proxies Can Help Protect Against DDoS Attacks
In today’s hyper-connected world, DDoS attacks have evolved from crude disruptions to sophisticated, AI-driven assaults. Botnets powered by machine learning algorithms can now launch attacks that are not only more powerful but also adapt to evade traditional defenses. For businesses in finance, gaming, e-commerce, and cloud services, staying ahead requires advanced security measures. Enter anti-DDoS proxy servers—a strategic layer of defense that filters malicious traffic before it reaches your core infrastructure, ensuring stability even under extreme pressure.
Understanding the Modern DDoS Threat
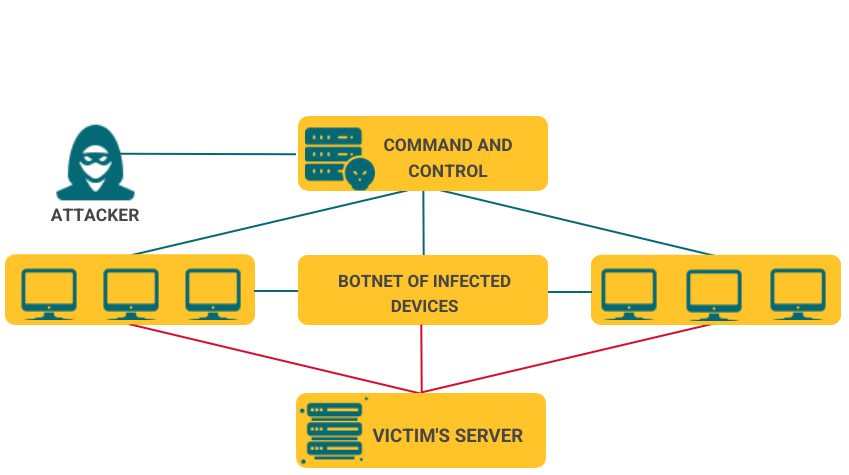
A Distributed Denial of Service (DDoS) attack is a cyberattack designed to overwhelm online services, making them unavailable to legitimate users. Attackers achieve this by hijacking networks of devices—from servers to IoT gadgets—forming a “botnet” that floods targets with fraudulent requests.
Why do these attacks happen? Motives range from competitive sabotage and financial extortion to political hacktivism and security testing. Regardless of intent, the impact is severe:
- Data Loss & Breaches: Can lead to information theft or system compromise.
- Skyrocketing Costs: Emergency security purchases and recovery efforts strain budgets.
- Reputational Damage: Frequent downtime erodes customer trust irreparably.
- Operational Standstill: An offline e-commerce site or SaaS platform means immediate revenue loss.
Consider this sobering example: In 2022, Google mitigated a record-breaking DDoS attack peaking at 46 million requests per second. The potential downtime cost? Estimates suggest nearly half a million dollars per hour. This underscores why proactive, multi-layered defense isn’t optional—it’s critical.
How Proxies Serve as Your First Line of Defense
A proxy server acts as a protective intermediary between the internet and your internal network. In the context of DDoS mitigation, its value is threefold:
- It Distributes Traffic & Balances Load: Incoming requests are intelligently routed across multiple servers, preventing any single point from becoming overwhelmed and failing.
- It Hides Your Real IP Address: By masking your origin server’s IP, proxies make it exponentially harder for attackers to target your infrastructure directly.
- It Filters Malicious Traffic: Proxies analyze incoming requests in real-time, blocking suspicious patterns, known bad IPs, and anomalous behavior before they reach your firewall.
Let’s dive deeper into these mechanisms.
1. Intelligent Load Distribution & Traffic Scrubbing
When a DDoS attack hits, it’s a flood of fake requests. A proxy server, especially a reverse proxy, acts as a “scrubbing center.”
How it works:
- A user (or bot) sends a request to your website.
- The request first hits the proxy server.
- The proxy analyzes it. If legitimate, it forwards the request to an available backend server. If malicious, it’s dropped.
- The response travels back through the same secure path.
The benefit: Your origin servers are shielded from the flood. Even under massive attack, legitimate users experience minimal disruption because the proxy absorbs and filters the brute force.
2. Concealing Your Digital Footprint
Think of your server’s IP address as your home address. If a threat actor knows it, they can attack it directly. A proxy server gives you a “PO Box.”
- To the outside world, only the proxy’s IP address is visible.
- All traffic flows through this secure gateway, keeping your actual server location and IP completely hidden.
This simple obfuscation is a powerful deterrent, forcing attackers to waste resources targeting your proxy’s defenses instead of your core systems.
3. Advanced Filtering & Behavioral Analysis
Modern proxies go beyond simple forwarding. They employ heuristics to identify and block threats:
- Rate Limiting: Automatically throttles or blocks IPs sending excessive requests.
- IP Blacklisting/Allowlisting: Instantly blocks traffic from known malicious networks or only allows trusted sources.
- Anomaly Detection: Flags traffic that deviates from established baselines (e.g., a sudden spike from a new country).
- Challenge Mechanisms: Deploys CAPTCHAs or JavaScript challenges to separate human users from automated bots.
Choosing the Right Proxy for DDoS Protection
Not all proxies are created equal for security purposes. The two most effective types are:
Reverse Proxies (The Go-To for DDoS Defense)
- How they work: Sit in front of your web servers, intercepting all client requests. They are the public face of your service.
- Best for: Protecting websites, APIs, and web applications.
- Key Advantage: Provide direct protection, load balancing, and can cache content to further reduce origin server load during an attack. Solutions like Cloudflare, Akamai, and Imperva are essentially sophisticated global reverse proxy networks.
Transparent Proxies
- How they work: Intercept traffic at the network level (often by an ISP or corporate firewall) without requiring client-side configuration.
- Best for: Internal corporate network security and ISP-level threat filtering.
- Key Advantage: Can provide a layer of inspection and filtering for all outbound/inbound traffic but offer less obscurity for the origin server than a reverse proxy.
| Proxy Type | Core Function | Ideal Use Case | Key Benefit for DDoS |
|---|---|---|---|
| Reverse Proxy | Intercepts & filters all incoming web traffic before it reaches the origin server. | Public websites, SaaS platforms, APIs. | Hides server IP, provides scalable load balancing, and performs deep traffic inspection. |
| Transparent Proxy | Filters traffic at the network gateway, often invisibly to end-users. | Corporate networks, ISP infrastructure. | Can block known attack vectors and malicious IPs at the network edge. |
Implementing an Anti-DDoS Proxy Strategy: A Practical Guide
Setting up an effective proxy defense involves more than just flipping a switch.
Step 1: Select Your Solution
- Managed Cloud Services (Recommended for most): Use providers like Cloudflare Pro/Enterprise, Akamai, or AWS Shield. They offer built-in, always-updated DDoS protection with global proxy networks.
- Self-Hosted Software: For maximum control, deploy solutions like NGINX or HAProxy as reverse proxies on your own infrastructure. This requires significant in-house expertise.
Step 2: Configure for Security
- Set Strict Filtering Rules: Implement geo-blocking for regions you don’t serve, create rate limits per IP, and integrate threat intelligence feeds.
- Enable Caching: Cache static content at the proxy layer to dramatically reduce the load on your origin servers during traffic spikes (malicious or legitimate).
- Tune Anomaly Detection: Define what “normal” traffic looks like for your business so the system can better identify anomalies.
Step 3: Integrate & Monitor
- Connect to Monitoring Tools: Use Grafana, Prometheus, or Datadog to monitor proxy traffic, request rates, and block counts in real-time.
- Set Up Alerts: Configure alerts for sudden traffic surges or rule triggers so your team can respond instantly.
- Plan for Scale: Ensure your proxy solution can automatically scale horizontally to handle volumetric attacks.
Beyond Proxies: A Layered Defense Mindset
While proxies are a formidable shield, true resilience comes from a defense-in-depth strategy:
- Keep Infrastructure Redundant: Ensure no single server or data center is a critical failure point.
- Maintain Robust Network Hygiene: Regularly update and patch all systems.
- Have an Incident Response Plan: Know exactly what to do and who to call when an attack is detected.
Final Word: Proxies as Your Strategic Security Partner
In an era of relentless and evolving cyber threats, relying solely on traditional firewalls is like locking your door but leaving the windows open. Proxy servers, particularly reverse proxies, provide the essential “bouncer” at the entrance to your digital property, scrutinizing every request before granting entry.
By strategically implementing a proxy-based defense layer, you’re not just buying time—you’re building a resilient infrastructure that maintains availability, protects customer trust, and safeguards your bottom line against one of the most common and disruptive threats on the internet today.
